A joint perspective on geo-fenced fraud, adaptive capture, and campaign disruption Fraud is the fastest growing attack surface,…

The Bolster Blog
Thought provoking blogs discussing recent trends on digital risk protection services, phishing protection, threat intelligence, artificial intelligence, machine learning, brand protection and more!
Recent Posts
Best Digital Brand Protection Services for Startups in 2026
You’re growing fast. Revenue is climbing, your brand is gaining recognition, and customers are starting to trust you. That’s exactly when the threats show up..
What is Online Brand Abuse (and 26 Ways to Stop it)
Online brand abuse is the unauthorized use of a brand’s identity, assets, or reputation across digital channels to deceive users, divert revenue, or cause reputational.

Buyer’s Guide: Purchasing a Brand Security Solution
Your brand is constantly under attack. To stay protected, you need an AI-powered brand security solution that keeps up with today’s AI-driven threats. Not sure what to look for? Use the Bolster AI Buyer’s Guide to evaluate your options.
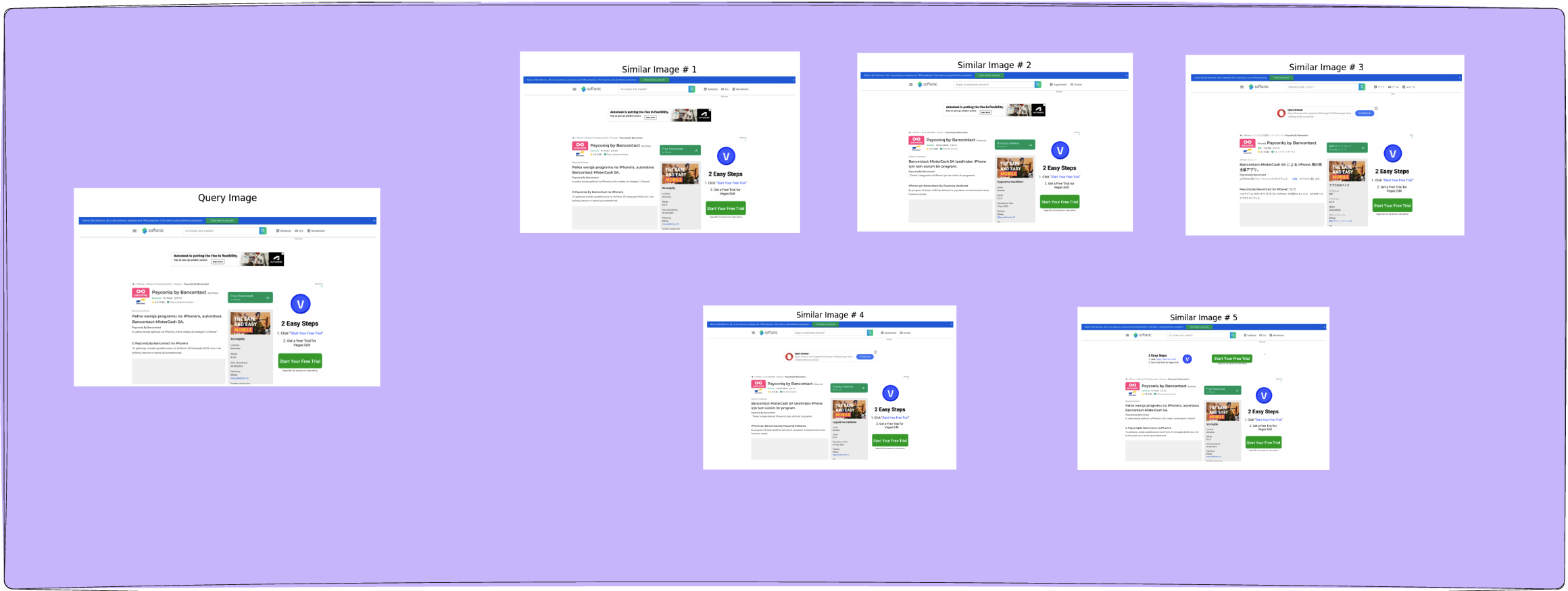
Image Similarity for Brand Detection: A Comparison Between BEiT, SWIN and ViT-MAE
Image similarity has emerged as one of the most powerful…
Identifying Compromised Antivirus Software & Fake Sites
Antivirus vendors have significantly been impacted by the latest phishing…
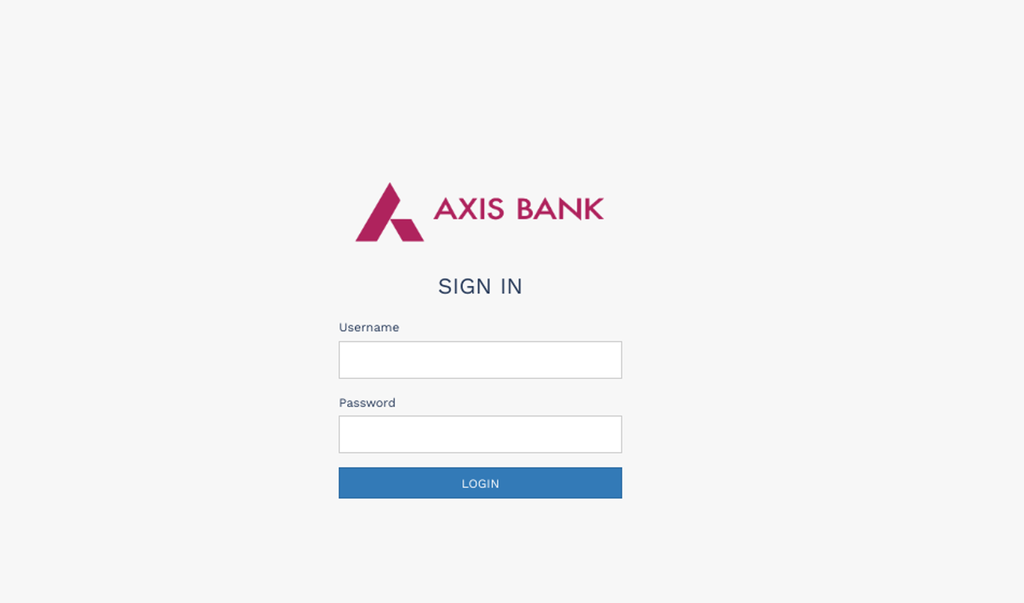
Dissecting the Phishing Kit behind the Axis Bank Reward Points Campaign
Phishing campaigns targeting banking and financial institutions have always been…
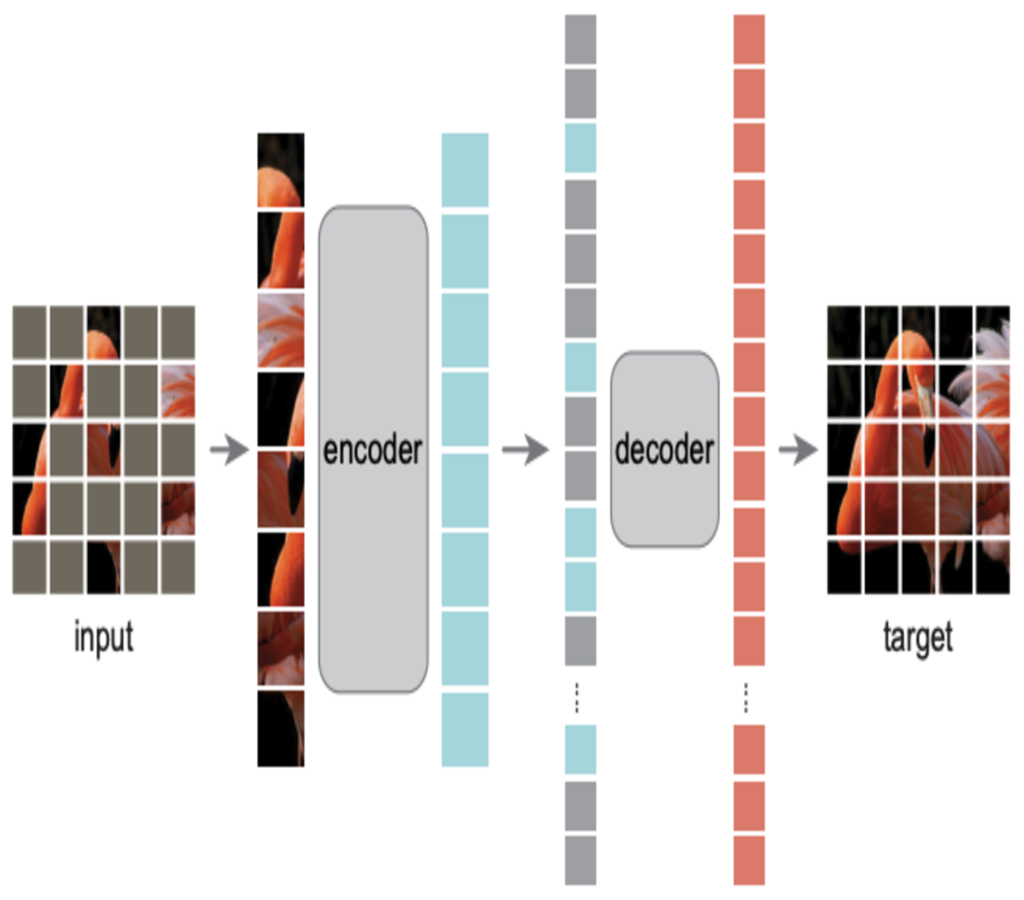
What is VIT-MAE? Scalable Learning for Vision Transformers.
Key Takeaways: Self-supervised vision framework combining Vision Transformers with masked…
A Global Crisis: What Companies Must Do to Avoid Legal Ramifications of Phishing Attacks
It wasn’t that long ago when phishing attacks were simply…
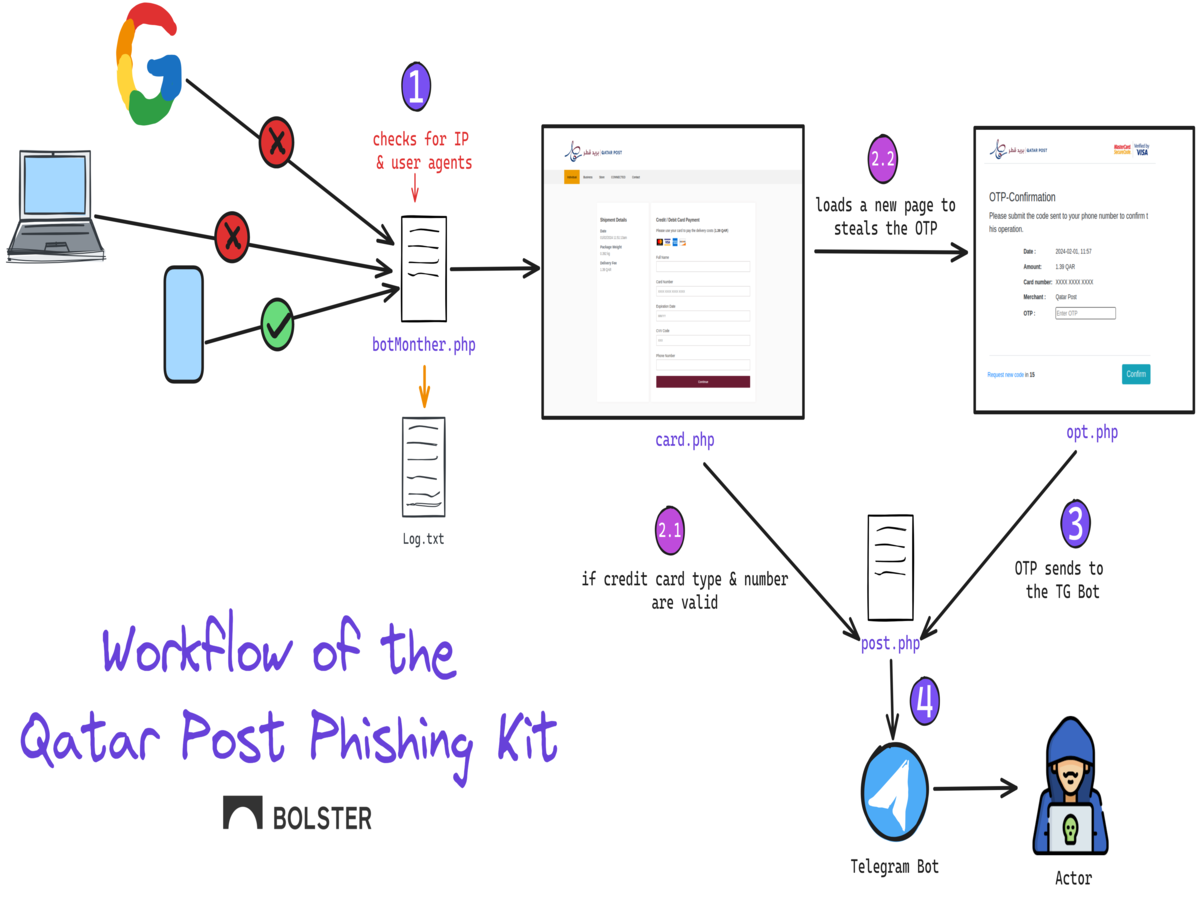
Dissecting the Newest Phishing Kit Targeting the Qatar Post
Name brand postal services have been increasingly targeted by phishing…
The Dark Underbelly of the Internet: Bulletproof Hosting and Phishing Epidemic
What is Bullet Proof Hosting [BPH]? Within the digital community,…
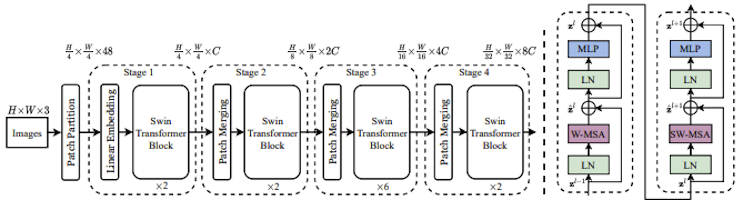
SWIN Transformers Explained: The Best of Two Worlds
Key Takeaways Swin Transformers processes images through shifted, localized windows…
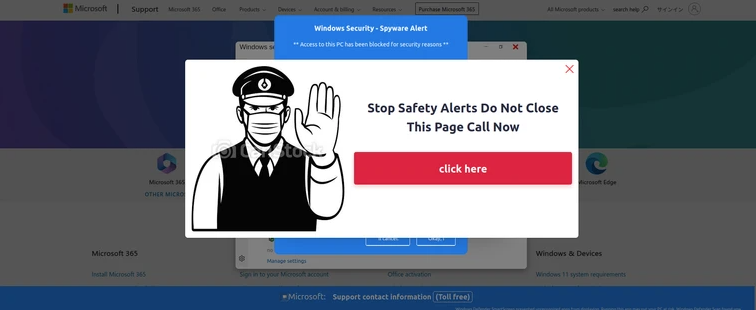
Analyzing Advanced Multi-Lingual Tech Support Phishing Kits Hosted on SaaS Providers
The Tech Support Scam consistently remains in the spotlight due…
Beyond Hashing: The Future of Anti-Phishing is Image Similarity Search
Computer vision modules are a critical component in a cybersecurity…
The Year in Review: Top 10 Scam Trends From 2023
In today’s increasingly digital world, cyber scams have become a…
How to Avoid Falling for Gift Card Scams This Holiday Season
The holiday season is an exciting time of year, bringing…