A joint perspective on geo-fenced fraud, adaptive capture, and campaign disruption Fraud is the fastest growing attack surface,…

The Bolster Blog
Thought provoking blogs discussing recent trends on digital risk protection services, phishing protection, threat intelligence, artificial intelligence, machine learning, brand protection and more!
Recent Posts
Best Digital Brand Protection Services for Startups in 2026
You’re growing fast. Revenue is climbing, your brand is gaining recognition, and customers are starting to trust you. That’s exactly when the threats show up..
What is Online Brand Abuse (and 26 Ways to Stop it)
Online brand abuse is the unauthorized use of a brand’s identity, assets, or reputation across digital channels to deceive users, divert revenue, or cause reputational.

Buyer’s Guide: Purchasing a Brand Security Solution
Your brand is constantly under attack. To stay protected, you need an AI-powered brand security solution that keeps up with today’s AI-driven threats. Not sure what to look for? Use the Bolster AI Buyer’s Guide to evaluate your options.
Copyright Infringement Examples: Lessons to Help You Protect Your Business
There are several famous copyright infringement examples, with perhaps the…
Bolster vs Zerofox: Comparing Brand Protection Solutions
Bolster vs. Competitors Bolster AI ZeroFox Automated Takedown < 24…
Detecting Deepfakes—How They Are Created & How to Spot Them
Key Takeaways: Analyze lip-syncing inconsistencies, unnatural blinking patterns, and facial…
Gray Market vs. Black Market: 5 Ways to Protect Your Business
Key Takeaways: Gray market sells authentic goods through unauthorized channels;…
Six Impersonation Attack Examples and How to Shield Your Business
Impersonation attacks are smarter and more deceptive than ever, with…
How a Massive Brand Impersonation Scam Campaign Targeted Popular Apparel Brands
Back in 2023, Bolster’s threat research team uncovered a widespread…
12 Top Brand Protection Strategies for 2026: Combat Evolving Digital Threats
In this updated guide, we walk through 12 core online…
Weekly News Roundup: Ransomware Skyrockets, Proofpoint Phishing Emails, and More
This week, we’ve seen some big headlines in terms of…
Proactive Defense Against BEC Attacks: How to Stay Ahead of the Scammers
Business Email Compromise (BEC) has become a significant threat to…
The Need for AI Threat Detection in the Modern Cybersecurity Landscape
Today’s cybersecurity landscape demands much more than traditional threat detection,…
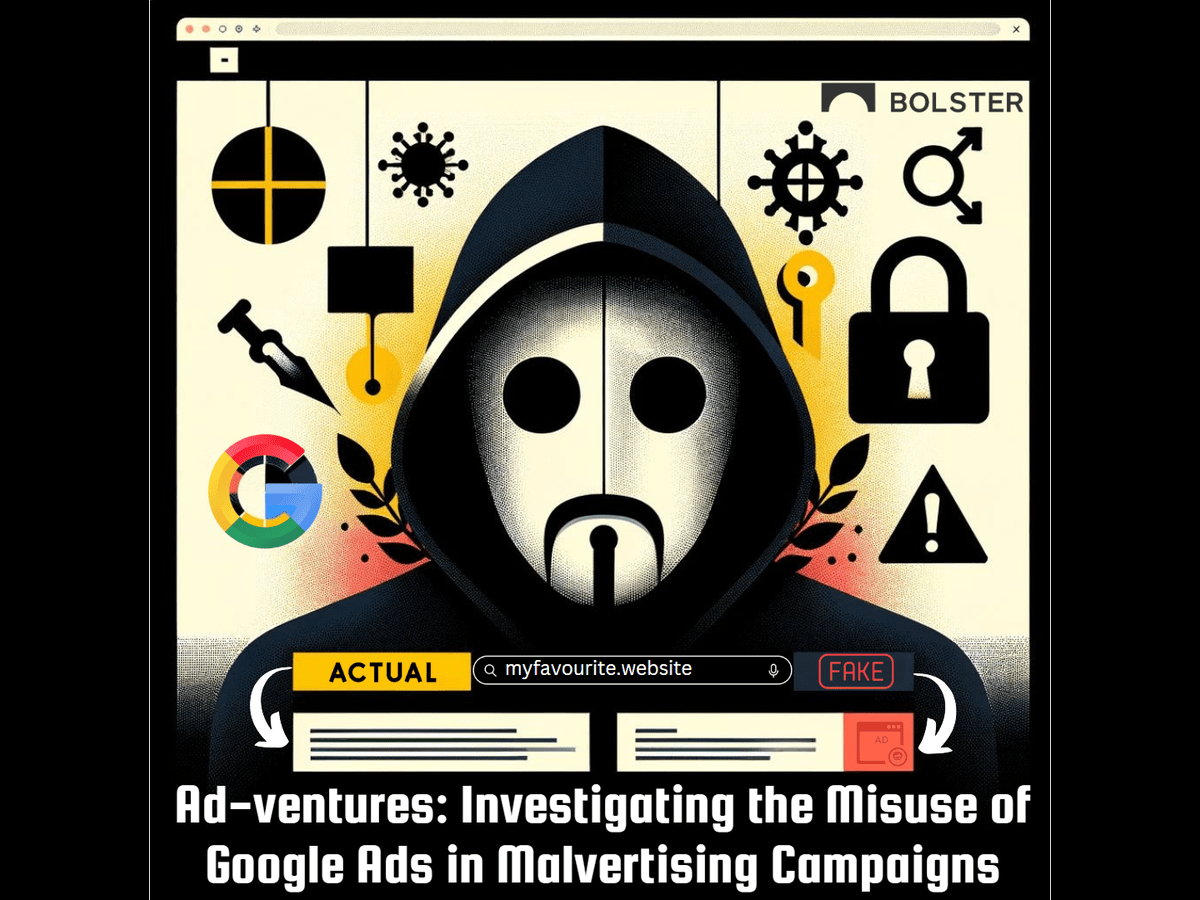
Ad-ventures: Investigating the Misuse of Google Ads in Malvertising Campaigns
In the sprawling extent of the internet, Google Ads has…