A joint perspective on geo-fenced fraud, adaptive capture, and campaign disruption Fraud is the fastest growing attack surface,…

The Bolster Blog
Thought provoking blogs discussing recent trends on digital risk protection services, phishing protection, threat intelligence, artificial intelligence, machine learning, brand protection and more!
Recent Posts
Best Digital Brand Protection Services for Startups in 2026
You’re growing fast. Revenue is climbing, your brand is gaining recognition, and customers are starting to trust you. That’s exactly when the threats show up..
What is Online Brand Abuse (and 26 Ways to Stop it)
Online brand abuse is the unauthorized use of a brand’s identity, assets, or reputation across digital channels to deceive users, divert revenue, or cause reputational.

Buyer’s Guide: Purchasing a Brand Security Solution
Your brand is constantly under attack. To stay protected, you need an AI-powered brand security solution that keeps up with today’s AI-driven threats. Not sure what to look for? Use the Bolster AI Buyer’s Guide to evaluate your options.
Image Tokenization: How Vision Transformers See the World
Key Takeaways Converts images into sequences of tokens representing image…
A Deep Dive into Evilginx
Key Takeaways: Evilginx is a Man-in-the-Middle phishing framework that proxies…
Bolster Launches New Phishing in Focus Report Highlighting Key Mid-Year Election Scams and Consumer-Focused Attacks
AI ignites an unprecedented surge in phishing attacks: See what…
Scammers Leveraging the Global CrowdStrike Outage
Scammers took only a few hours to jump onto the…
Taylor Swift Ticket Scams: Don't Let EU Tour Phishing Nightmares Ruin Your Wildest Dreams
Fans all around Europe are clamoring to see their favorite…
From FOMO to Fraud: Understanding Crypto Scams in Market Booms
Fear of Missing Out in the cryptocurrency world can lead…
Navigating Tax Season Safely: Understanding the Threat of IRS Scams and Phishing Operations
The sophistication of IRS scams and phishing attempts targeting taxpayers…
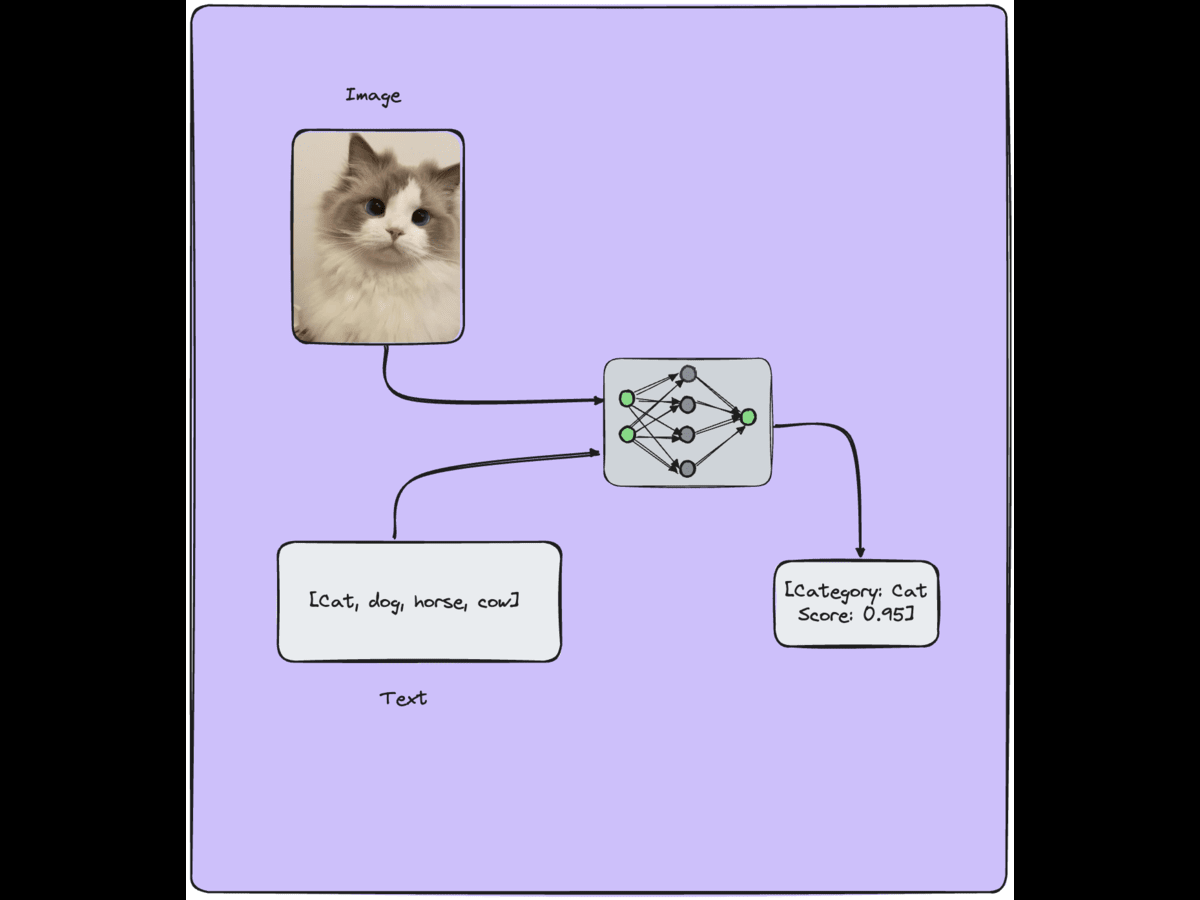
Vision Language Models Applications & Learning Strategies
Vision Language Models (VLMs) have applications in various fields, including…
Ad-ventures: Investigating the Misuse of Google Ads in Malvertising Campaigns
In the sprawling extent of the internet, Google Ads has…
Stealer Logs & The Threat That is Compromising Security
Beyond the conventional concerns of viruses, spyware, and phishing scams,…
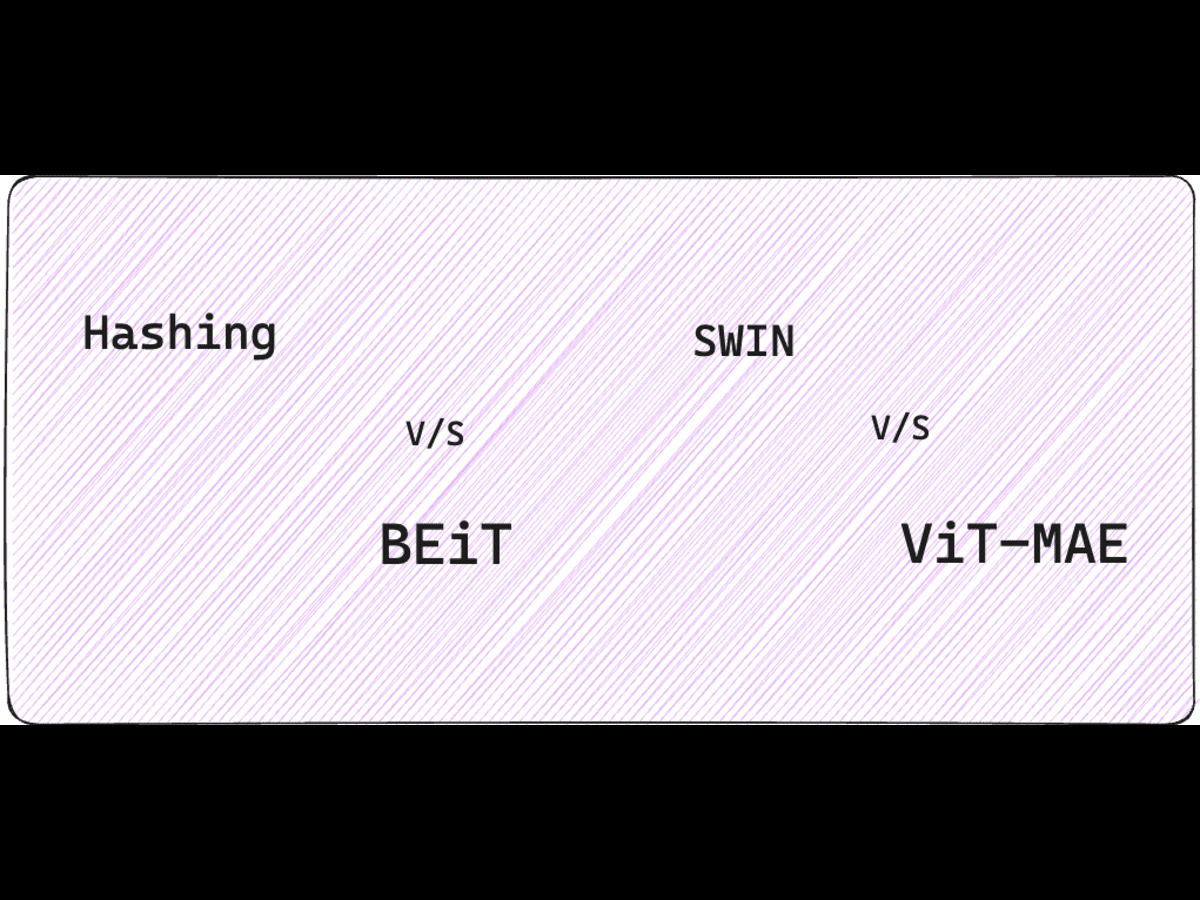
Image Similarity for Brand Detection: A Comparison Between BEiT, SWIN and ViT-MAE
Image similarity has emerged as one of the most powerful…
Identifying Compromised Antivirus Software & Fake Sites
Antivirus vendors have significantly been impacted by the latest phishing…