A joint perspective on geo-fenced fraud, adaptive capture, and campaign disruption Fraud is the fastest growing attack surface,…

The Bolster Blog
Thought provoking blogs discussing recent trends on digital risk protection services, phishing protection, threat intelligence, artificial intelligence, machine learning, brand protection and more!
Recent Posts
Best Digital Brand Protection Services for Startups in 2026
You’re growing fast. Revenue is climbing, your brand is gaining recognition, and customers are starting to trust you. That’s exactly when the threats show up..
What is Online Brand Abuse (and 26 Ways to Stop it)
Online brand abuse is the unauthorized use of a brand’s identity, assets, or reputation across digital channels to deceive users, divert revenue, or cause reputational.

Buyer’s Guide: Purchasing a Brand Security Solution
Your brand is constantly under attack. To stay protected, you need an AI-powered brand security solution that keeps up with today’s AI-driven threats. Not sure what to look for? Use the Bolster AI Buyer’s Guide to evaluate your options.
How to File an Instagram DMCA Takedown: Stop Copyright Infringement on Instagram
You’re scrolling through Instagram when you spot it: your brand’s…
Mobile App Fraud Detection: How Fake Apps Undermine Trust, Revenue, and Security
Mobile apps have become one of the most trusted ways…
How to Do a Dark Web Scan: The Complete Playbook
Your organization’s credentials are probably already on the dark web;…
Best Phishing Email Tools: Detection & Automated Takedowns
Phishing attacks cost organizations an average of $4.88 million per…
Advanced Threat Protection Solutions: Stopping Attacks Before They Start
Cyber attacks are surging at an unprecedented pace. According to…
Detect and Kill AI Phishing: A 6-Step Defense Guide
The phishing landscape has transformed dramatically. What once required manual…
Call Forwarding Scams & How to Protect Yourself from Dangerous Fraud
Key Takeaways: Scammers trick victims into dialing codes like *401#…
7 Tips to Prevent Cybersquatting Before It Damages Your Brand
Cybersquatting, a form of domain name abuse, refers to…
Detecting Deepfakes—How They Are Created & How to Spot Them
Key Takeaways: Analyze lip-syncing inconsistencies, unnatural blinking patterns, and facial…
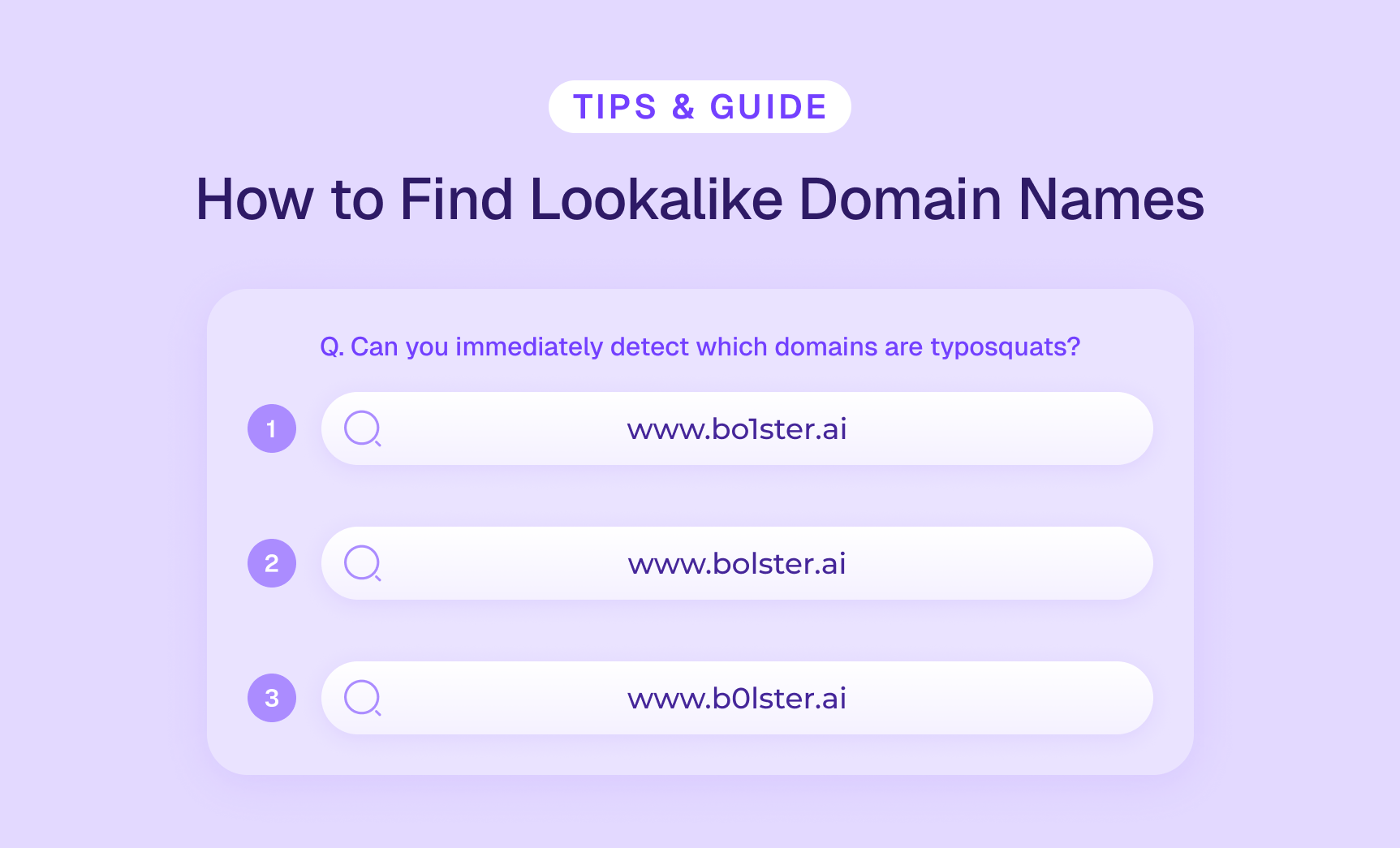
Lookalike Domain Monitoring & How to Find Similar Domain Names
Key Takeaways: Similar domains are fraudulent domains mimicking legitimate ones…
So, What Does a Brand Protection Team Do Anyways?
Your brand is everywhere — on your website, across social…
Gray Market vs. Black Market: 5 Ways to Protect Your Business
Key Takeaways: Gray market sells authentic goods through unauthorized channels;…