In an interconnected digital world, the threat of cyberattacks continues…
118 results for keyword "Tips & Guides"
Credential Phishing Prevention & 10 Steps to Safeguarding Your Digital Identity
Key Takeaways About Credential Phishing Attackers trick users into providing…
Dealing with Imposter Accounts on Social Media
Picture yourself as an IT security and risk management professional…
RSA Conference 2024: Bolster Recap and Key Takeaways
Security conferences are a great chance to stay on top…
How AI Email Security Safeguards Your Organization’s Communication Efforts
Even with the many apps, social media platforms, and other…
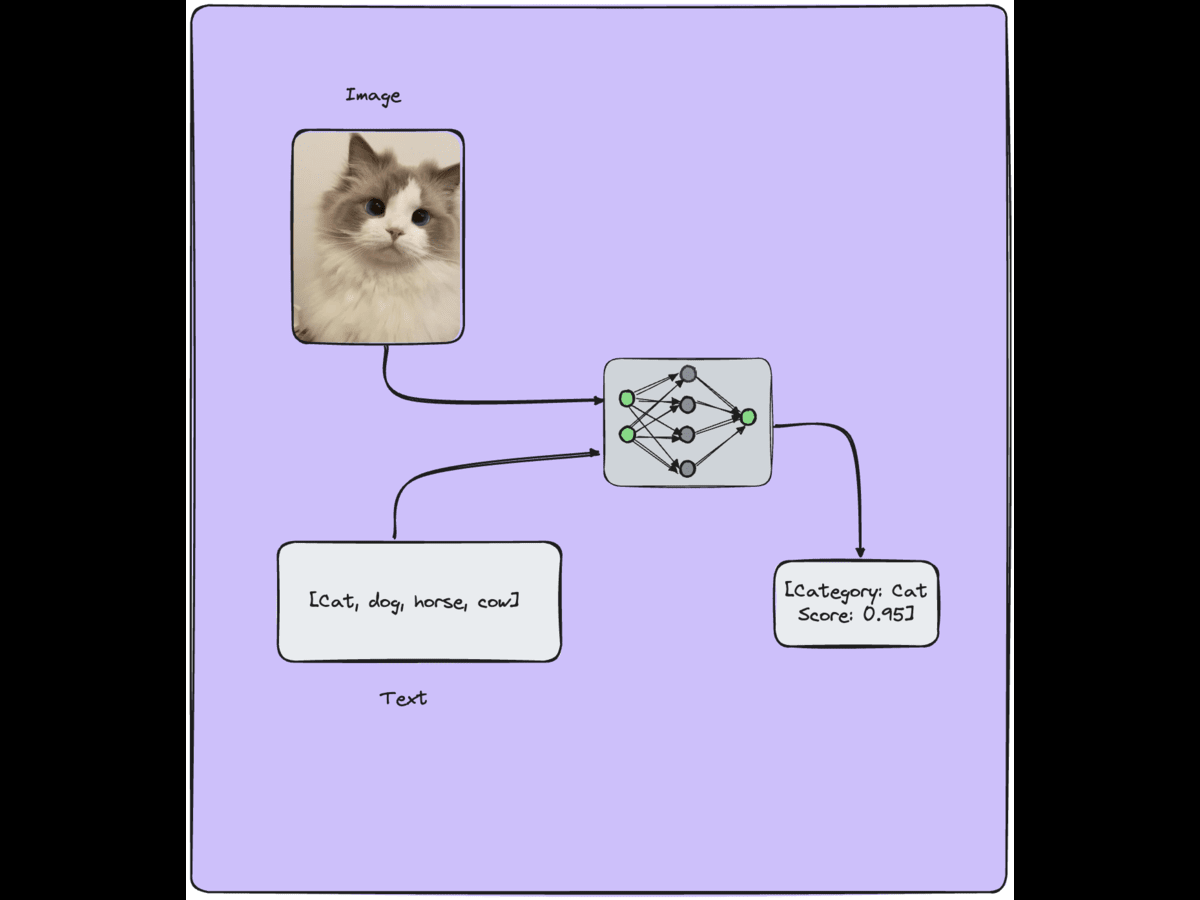
Vision Language Models Applications & Learning Strategies
Vision Language Models (VLMs) have applications in various fields, including…
The Need for AI Threat Detection in the Modern Cybersecurity Landscape
Today’s cybersecurity landscape demands much more than traditional threat detection,…
Digital Risk Monitoring Importance is Growing Faster Than Ever
Key Takeaways About: Digital Risk Monitoring: DRM automates continuous scanning…
2024 State of Phishing & Online Scams: Statistics, Facts, Trends & Recommendations
From prompt responses to self-driving cars, 2023 felt the significant…
Strengthening Singapore’s Digital Defenses: A Deep Dive into Anti-Phishing Regulations
The rise in phishing attacks has become a global concern,…
A Global Crisis: What Companies Must Do to Avoid Legal Ramifications of Phishing Attacks
It wasn’t that long ago when phishing attacks were simply…
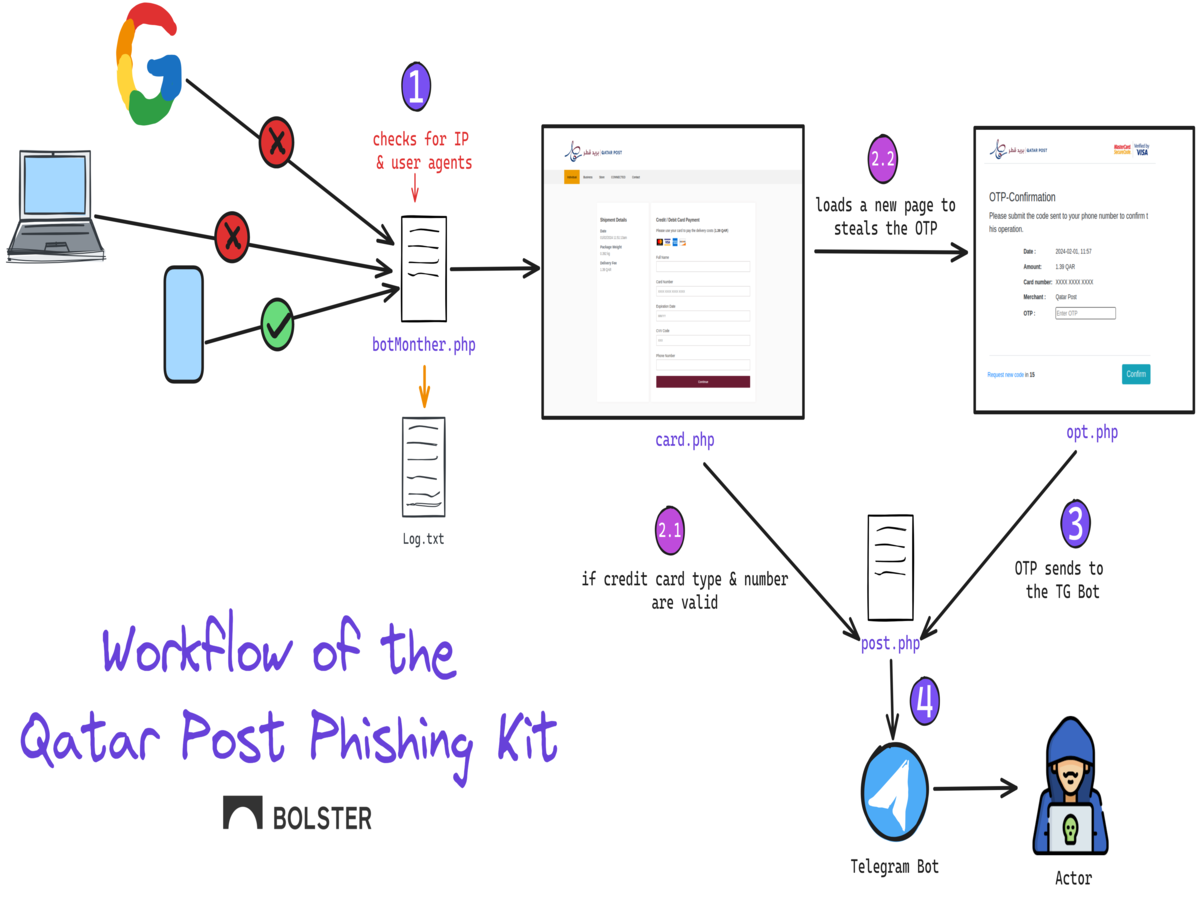
Dissecting the Newest Phishing Kit Targeting the Qatar Post
Name brand postal services have been increasingly targeted by phishing…