You’re scrolling through Instagram when you spot it: your brand’s…
118 results for keyword "Tips & Guides"
Mobile App Fraud Detection: How Fake Apps Undermine Trust, Revenue, and Security
Mobile apps have become one of the most trusted ways…
How to Do a Dark Web Scan: The Complete Playbook
Your organization’s credentials are probably already on the dark web;…
Best Phishing Email Tools: Detection & Automated Takedowns
Phishing attacks cost organizations an average of $4.88 million per…
Advanced Threat Protection Solutions: Stopping Attacks Before They Start
Cyber attacks are surging at an unprecedented pace. According to…
Detect and Kill AI Phishing: A 6-Step Defense Guide
The phishing landscape has transformed dramatically. What once required manual…
Call Forwarding Scams & How to Protect Yourself from Dangerous Fraud
Key Takeaways: Scammers trick victims into dialing codes like *401#…
7 Tips to Prevent Cybersquatting Before It Damages Your Brand
Cybersquatting, a form of domain name abuse, refers to…
Detecting Deepfakes—How They Are Created & How to Spot Them
Key Takeaways: Analyze lip-syncing inconsistencies, unnatural blinking patterns, and facial…
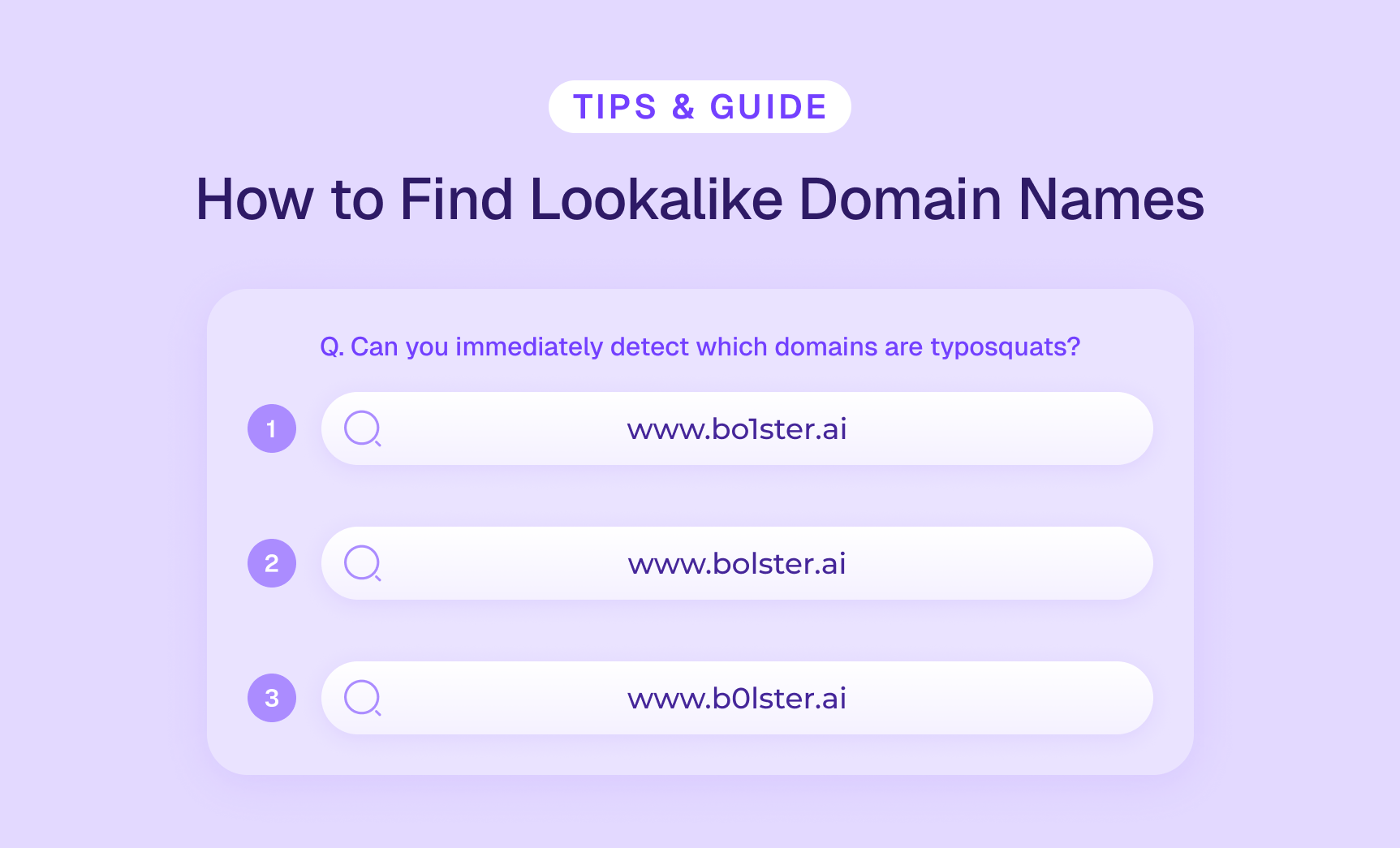
Lookalike Domain Monitoring & How to Find Similar Domain Names
Key Takeaways: Similar domains are fraudulent domains mimicking legitimate ones…
So, What Does a Brand Protection Team Do Anyways?
Your brand is everywhere — on your website, across social…
Gray Market vs. Black Market: 5 Ways to Protect Your Business
Key Takeaways: Gray market sells authentic goods through unauthorized channels;…