In the sprawling extent of the internet, Google Ads has…
88 results for keyword "Research Labs"
Stealer Logs & The Threat That is Compromising Security
Beyond the conventional concerns of viruses, spyware, and phishing scams,…
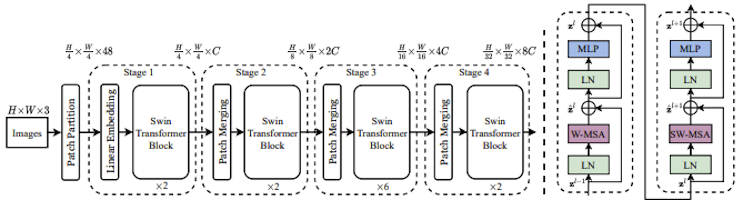
Image Similarity for Brand Detection: A Comparison Between BEiT, SWIN and ViT-MAE
Image similarity has emerged as one of the most powerful…
Identifying Compromised Antivirus Software & Fake Sites
Antivirus vendors have significantly been impacted by the latest phishing…
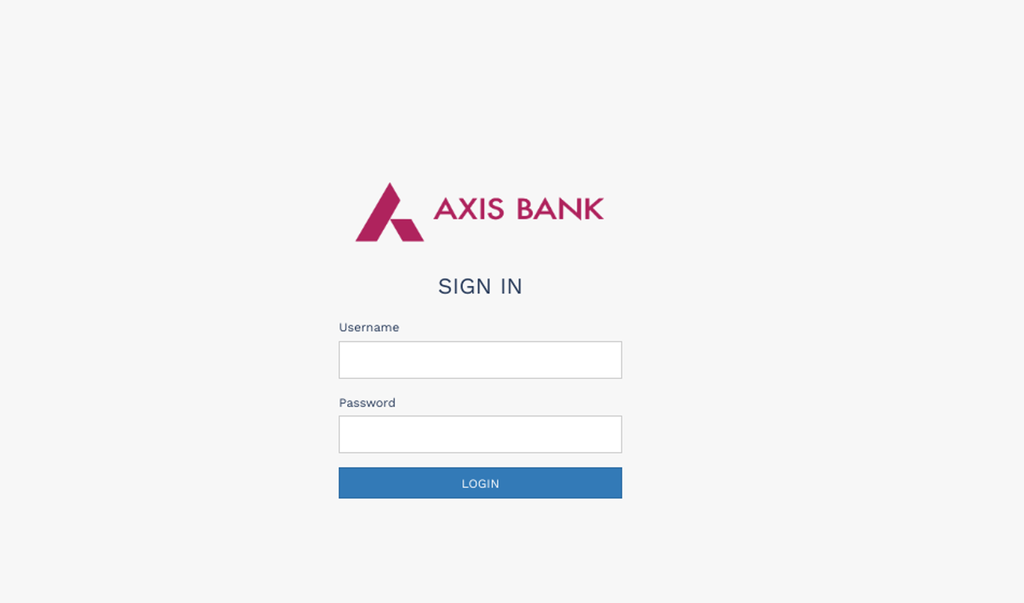
Dissecting the Phishing Kit behind the Axis Bank Reward Points Campaign
Phishing campaigns targeting banking and financial institutions have always been…
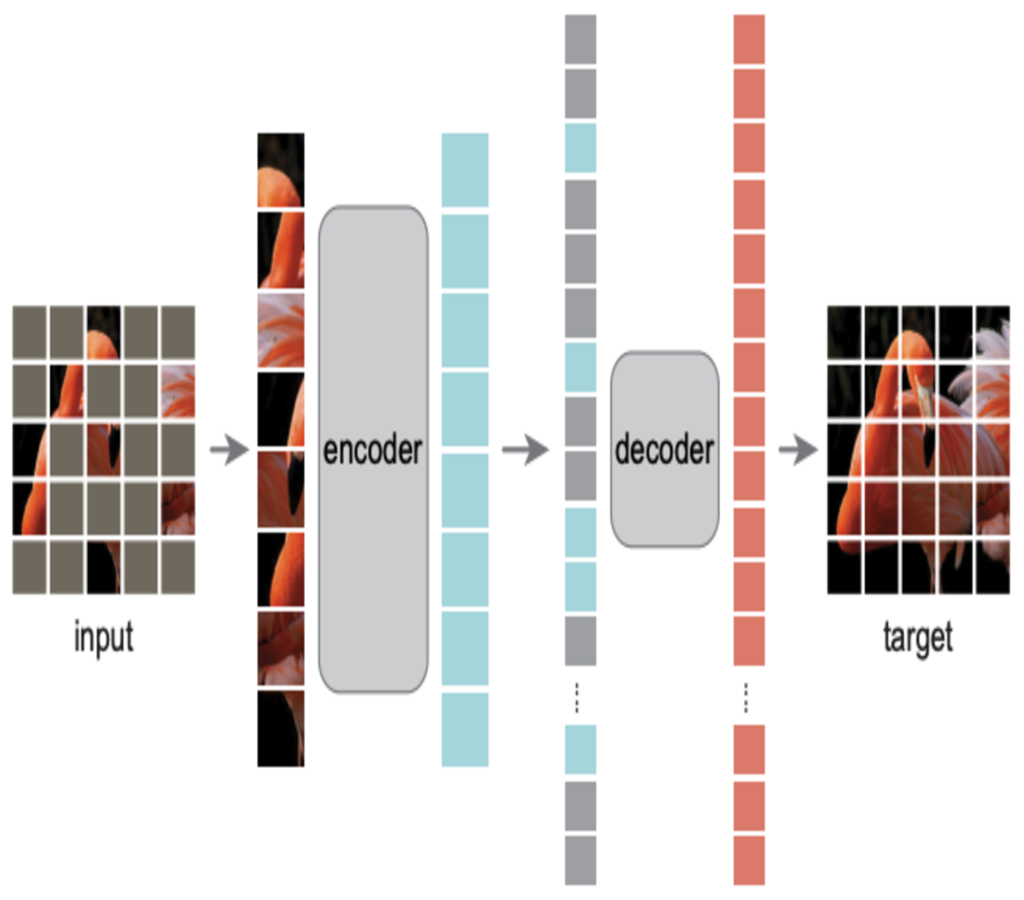
What is VIT-MAE? Scalable Learning for Vision Transformers.
Key Takeaways: Self-supervised vision framework combining Vision Transformers with masked…
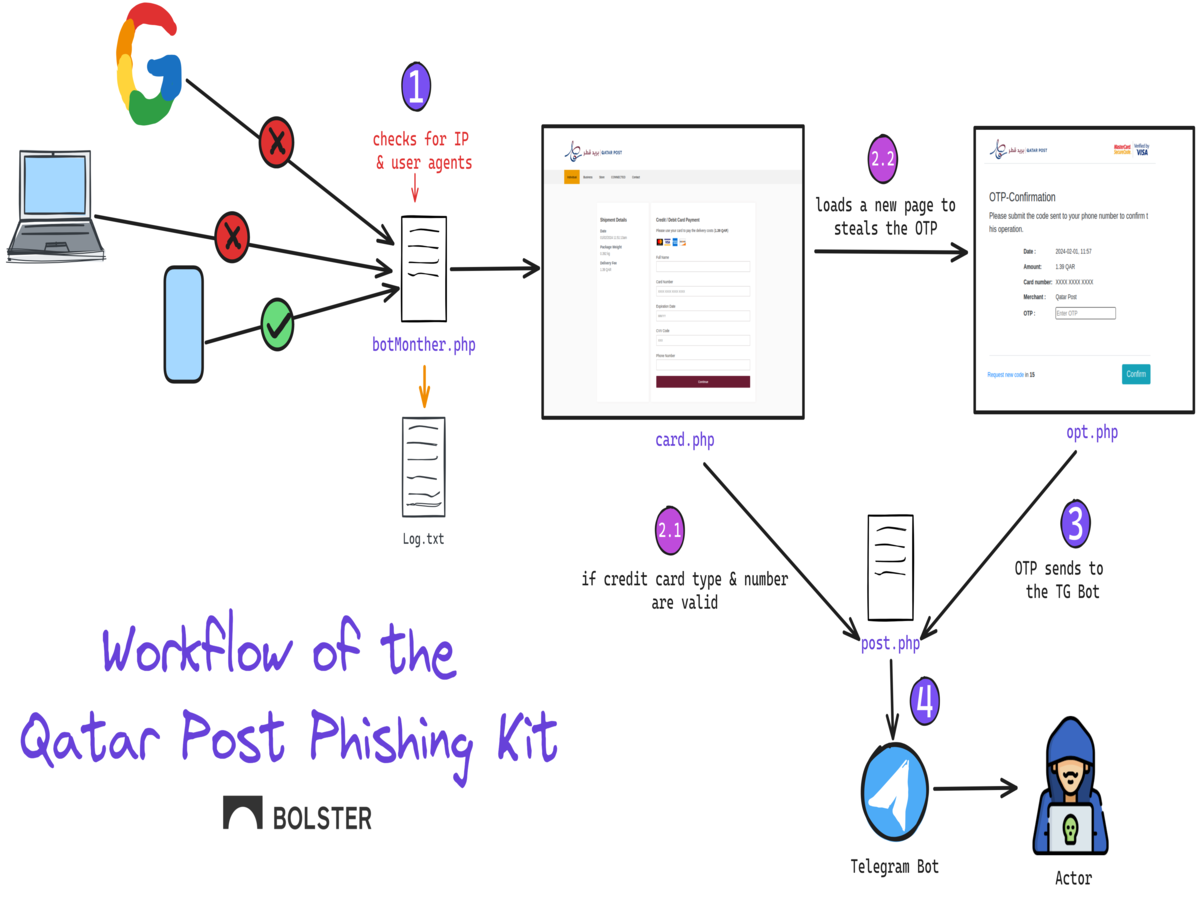
Dissecting the Newest Phishing Kit Targeting the Qatar Post
Name brand postal services have been increasingly targeted by phishing…
The Dark Underbelly of the Internet: Bulletproof Hosting and Phishing Epidemic
What is Bullet Proof Hosting [BPH]? Within the digital community,…
SWIN Transformers Explained: The Best of Two Worlds
Key Takeaways Swin Transformers processes images through shifted, localized windows…
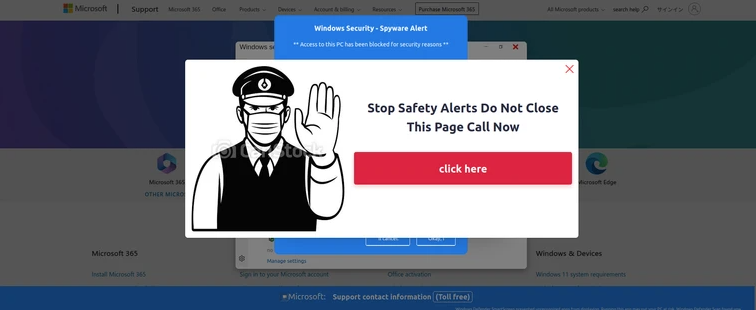
Analyzing Advanced Multi-Lingual Tech Support Phishing Kits Hosted on SaaS Providers
The Tech Support Scam consistently remains in the spotlight due…
Beyond Hashing: The Future of Anti-Phishing is Image Similarity Search
Computer vision modules are a critical component in a cybersecurity…
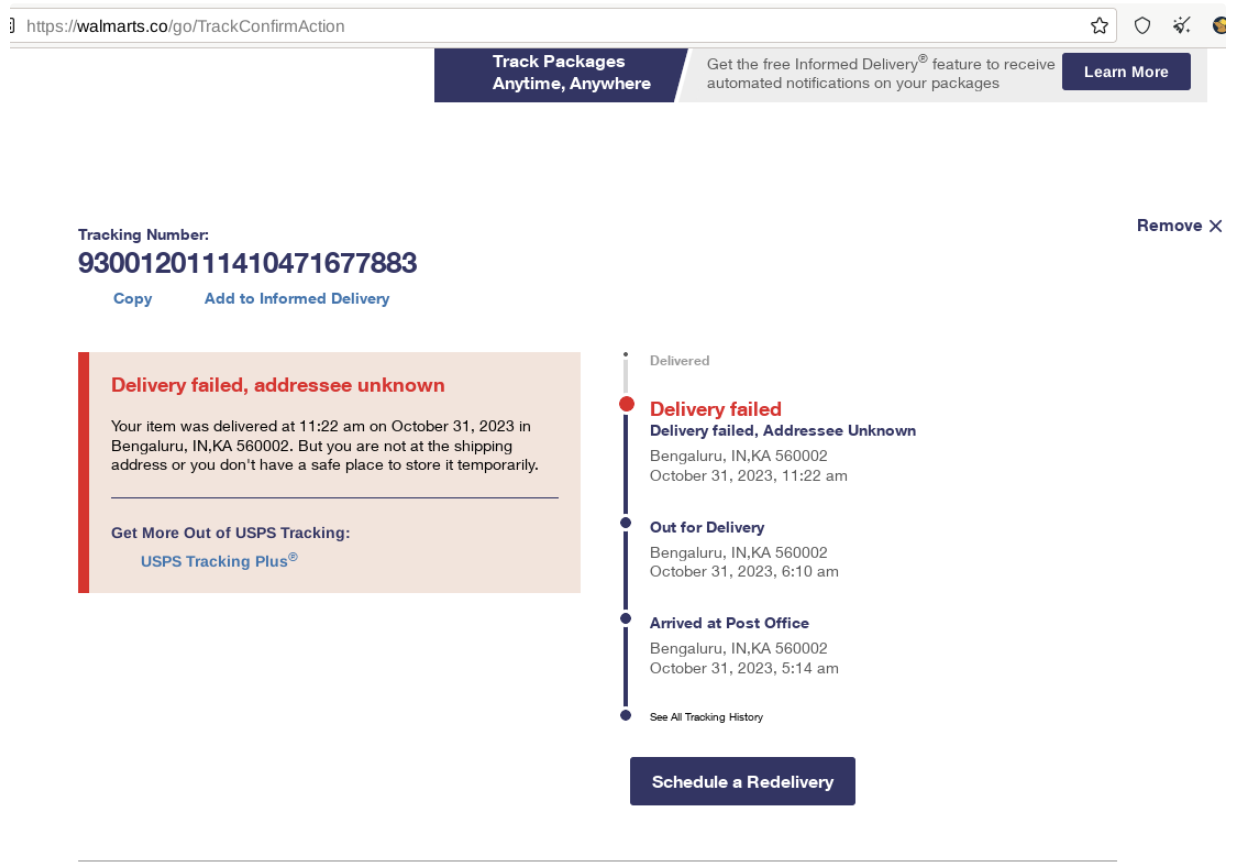
Vast USPS Delivery Phishing Campaign Sees Threat Actors Abusing Freemium Dynamic DNS and SaaS Providers
You may be familiar with the common phishing tactics like…