AI agents are getting smarter. Phishing kits are getting smarter, too. But the most exploited vulnerability in cybersecurity hasn’t changed: human behavior.
Threat actors know this. They time their campaigns around high-trust moments like tax season, holiday sales, and product launches, then impersonate the brands people rely on most. As the Bolster AI 2026 Fraud Trends Report found, brands are now receiving over 30,000 customer-submitted “is this real?” reports per month. In that context, the ability to accurately analyze a URL isn’t just a nice-to-have. It’s a frontline skill.
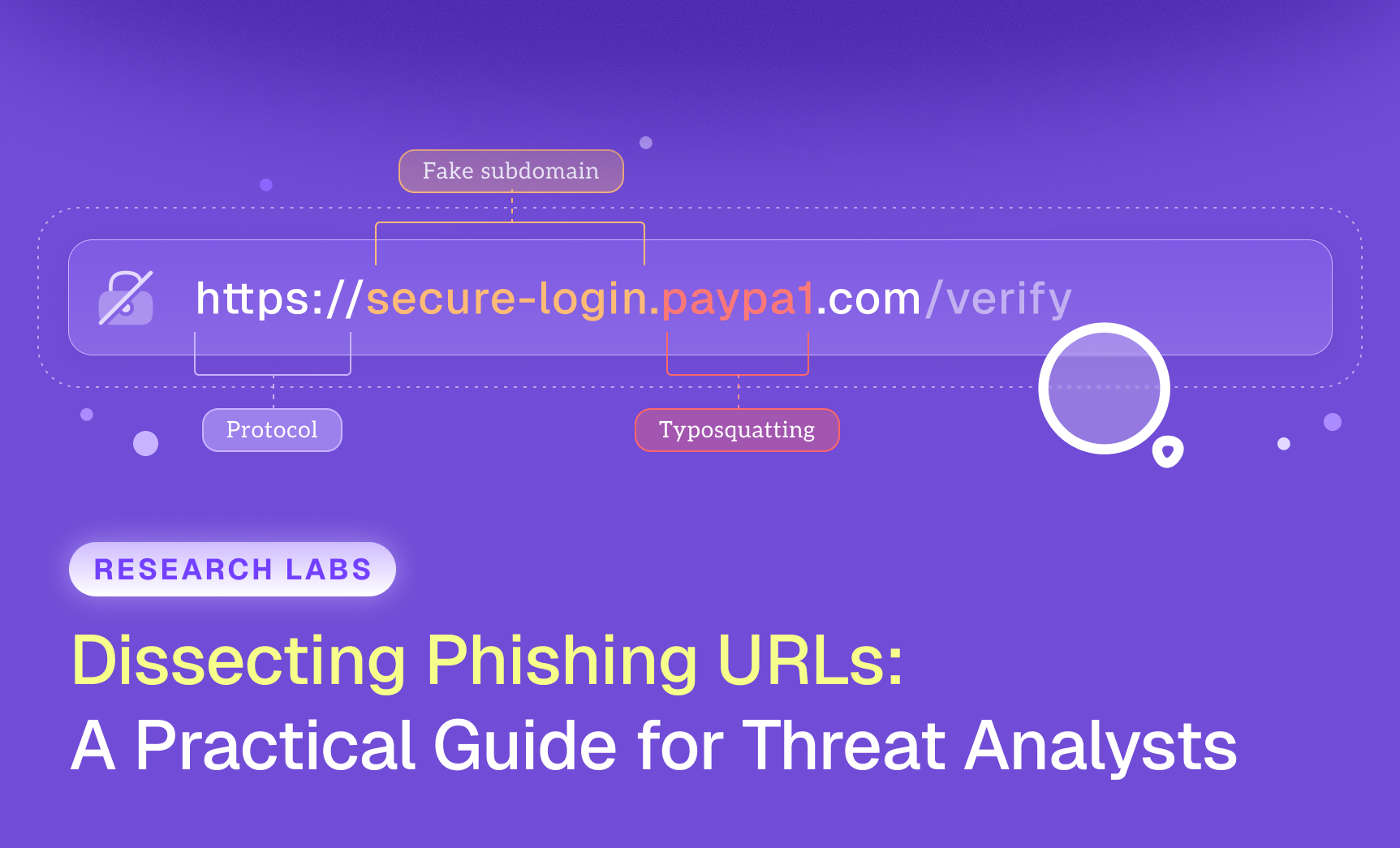
This guide breaks down a practical, step-by-step framework for dissecting phishing URLs and identifying malicious indicators before they reach your customers.
Why URL Analysis Still Matters in the AI Era
For a threat hunter or SOC analyst, a URL isn’t just a link. It’s a technical artifact that exposes infrastructure decisions, attacker maturity, campaign scale, and sometimes operational mistakes.
Careful URL dissection helps analysts quickly determine whether they’re looking at a low-effort phishing attempt on a free subdomain, a typosquatted domain impersonating a known brand, or a coordinated campaign using redirect chains and cloaking.
URL structure often reveals attacker sophistication. Less experienced operators tend to use obvious brand keywords and sloppy domains. Advanced actors deploy layered subdomains, encoded parameters, traffic distribution systems (TDS), and geotargeted redirection.
Encoded strings like Base64 parameters, hex values, session tokens, or redirect identifiers may look like noise to the average user. To a trained analyst, they expose redirection logic, credential harvesting endpoints, and campaign tracking mechanisms.
AI has raised the stakes. Threat actors now use it to generate realistic phishing templates, localize content at scale, mutate domain patterns automatically, and deploy kits across thousands of URLs. Bolster AI’s research team tracked 12 million malicious domains in a single year. It’s increasingly common to see campaigns where thousands of unique source URLs funnel to a single harvesting endpoint, rendering simple domain blocking ineffective and complicating takedown operations.
Structured URL analysis isn’t a basic security check anymore. It’s a foundational investigative skill.
Step-by-Step URL Dissection Framework
A structured approach helps analysts move past surface-level assumptions. Instead of reacting instinctively, break the URL into components and evaluate each layer.
Note: The URLs used in the examples below are hypothetical and created for educational purposes only. They do not represent real websites or active phishing campaigns.
Step 1: Identify the Root Domain
This is the most important step. Threat actors deliberately structure URLs to obscure the real domain, often placing trusted brand names at the beginning of the link. This is a core tactic in impersonation attacks.
Rookie threat actor example:
It looks brand-related at first glance. But the root domain is netflixsupportlogin.com. That’s a textbook case of brand keyword stuffing.
Advanced threat actor example:
Here, the attacker places “netflix.com” at the beginning to mislead users visually. The actual root domain is accountsecurityupdate.com. Everything to the left of that is a subdomain the attacker controls.
For non-technical users, telling these apart is extremely difficult. That’s why analysts must always isolate and verify the true root domain first. Free tools like CheckPhish can help quickly scan and classify suspicious URLs in real time.
Step 2: Examine Domain Characteristics
Once you’ve isolated the root domain, assess it against these criteria:
- Is it a typosquatted version of a known brand?
- Does it use excessive brand keywords?
- Is the TLD unusual or commonly abused?
- How old is the domain?
Recently registered domains are a red flag. They’re frequently created specifically for phishing operations. Domain age and registration patterns provide immediate context about a campaign’s intent and expected lifespan. Automated domain monitoring can flag these registrations in real time before they go active.
Step 3: Inspect the Path and Parameters
Suspicious URL paths often include /login, /auth-update, /verify, or /update-account, especially when they appear on domains unrelated to the legitimate brand.
Attackers frequently encode parameters using Base64 or hexadecimal strings to hide redirect paths, tracking identifiers, or credential collection endpoints. These strings may look random, but decoding them can expose how the phishing infrastructure routes victims.
Step 4: Observe the Behavior
Static analysis only gets you so far. Always test the URL in a controlled environment to observe its live behavior.
Key questions to answer:
- Does it redirect immediately?
- Are there multiple layers of redirection?
- Does it cloak content from scanners?
- Is it accessible only from certain IP ranges, user agents, or operating systems?
Behavioral testing often confirms whether the URL is part of a larger, coordinated campaign, not just an isolated attempt. For a deeper look at how phishing kit infrastructure works under the hood, see our analysis of how phishing kit creators operate and even steal from each other.
Real-World Phishing Tactics in 2025
Phishing has evolved far beyond the crude, typo-riddled emails of a decade ago. Today’s attackers are organized, automated, and highly effective because they mimic legitimate corporate processes almost perfectly.
Threat actors frequently impersonate brands during high-trust periods: tax deadlines, holiday shopping events, new product launches, and major sales. The emails are convincing. Password reset requests, payment failure notices, delivery confirmations, account verification prompts. And they’re getting harder to spot. The Bolster AI Phishing in Focus report found that over 38,000 new phishing sites were launching per day during peak periods.
AI-powered phishing kits have accelerated this trend. They generate grammatically correct emails across multiple languages and create landing pages that closely replicate legitimate corporate sites. Traditional phishing indicators like misspellings, broken layouts, and awkward phrasing are disappearing.
Phishing isn’t a low-effort scam anymore. It’s a scalable operation.
Common Mistakes Analysts Make
From a brand protection perspective, the gap between basic detection and meaningful disruption comes down to analytical discipline. Here are the pitfalls that trip up even experienced teams:
- Treating HTTPS as a trust signal. Encryption does not equal legitimacy.
- Failing to isolate the true root domain. Subdomains can be weaponized easily.
- Ignoring domain registration intelligence. Domain age, registrar patterns, and infrastructure reuse reveal campaigns.
- Overlooking redirect chains. The entry URL may only be the first stage.
- Not accounting for cloaking. Campaigns routinely hide payloads from scanners.
- Responding tactically instead of strategically. Blocking individual URLs instead of identifying infrastructure clusters. (Speed matters here. Every hour a phishing site stays live, attackers harvest more credentials.)
Human Judgment Is Still the Firewall
AI-driven detection systems and automated scanning keep improving. But phishing campaigns remain effective because they exploit human behavior, not just technical vulnerabilities.
Threat actors continuously rotate domains, deploy cloaking mechanisms, and mutate phishing infrastructure using AI. Viewed individually, these artifacts may appear unrelated. But structured human analysis connects the dots, identifying shared infrastructure, campaign patterns, and brand impersonation tactics that automation alone can miss.
One financial institution reduced its phishing response time from 32 days to 36 hours by combining AI-powered detection with disciplined human analysis. The persistent threat actors targeting their brand simply moved on to easier targets.
In a landscape increasingly shaped by automation, the role of a skilled analyst becomes more critical, not less. Human judgment, contextual awareness, and investigative reasoning remain the strongest defenses against modern phishing operations.
Bolster AI combines AI-powered detection with expert human analysis to identify and take down phishing campaigns at scale. Request a demo to see how we protect your brand from impersonation threats.