Online shopping scams are supposed to be easy to spot: a fake storefront, too-good-to-be-true discounts, and a domain that disappears within days. That’s the conventional wisdom, at least.
But Bolster AI’s research team has been tracking a new breed of e-commerce fraud that throws that assumption out the window. These aren’t sloppy copycats. They’re sophisticated impersonation operations that use geo-IP filtering, mobile user-agent enforcement, and paid ad campaign gating to stay invisible to traditional detection tools while remaining fully operational for their intended victims.
In other words, if you’re looking for them the way most brand protection teams do, you won’t find them.
What These Scam Sites Actually Look Like (When They Want You to See Them)
When Bolster AI’s researchers first accessed domains associated with this fraud framework, the sites appeared harmless. Generic e-commerce templates. Incomplete placeholder pages. Nothing that would trigger a brand monitoring alert or raise red flags during a routine investigation.
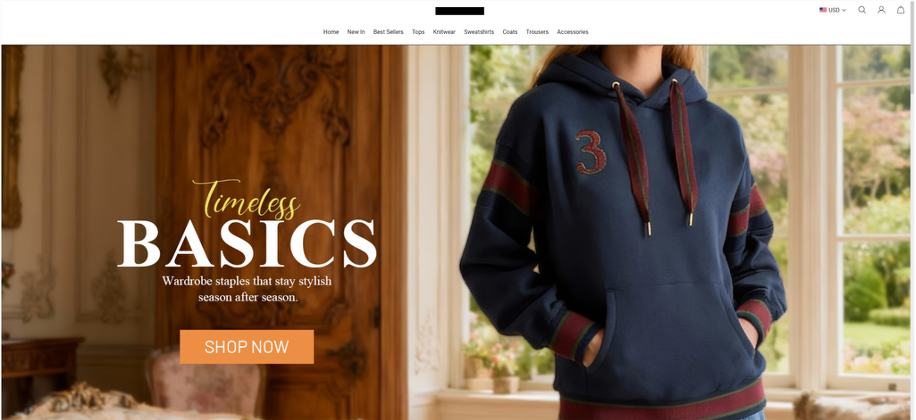
Generic Store Front
That’s by design.
The impersonation content only appears when three specific conditions are met simultaneously:
- Mobile user-agent specificity. The fraudulent storefront is gated behind iPhone user-agent profiles. Visit from a desktop browser and you’ll see nothing suspicious.
- Geo-IP targeting. Fraud exposure is restricted to specific geographic regions that align with the scammer’s ad targeting. Scanning from outside those regions returns the benign fallback page.
- Ad campaign parameters in the URL. The branded impersonation storefront only activates when the URL contains campaign parameters consistent with paid ad traffic, particularly from platforms like TikTok.
Accessing the same content without campaign parameter on US proxy using iPhone
Miss any one of those three conditions, and the site defaults to its innocent-looking cover. This isn’t a bug in the scam. It’s the scam’s most important feature.
Paid Ads Aren’t Just Driving Traffic. They’re Unlocking the Fraud
This is where it gets especially interesting. The campaign landing pages use URL structures that mimic legitimate e-commerce advertising flows, complete with standardized UTM fields and platform click identifiers. A sanitized example looks something like this:
/products?handler=best-seller&utm_source={platform}&utm_medium=paid
&utm_id={numeric_id}&utm_campaign={campaign_name}&{platform_click_id}
These URLs are engineered to blend into normal advertising telemetry. But they’re not just tracking artifacts. This aligns with findings from Bolster AI’s 2026 Fraud Trends report.
Bolster AI’s controlled testing confirmed that these campaign parameters are part of the conditional exposure logic itself. Without them, the fraudulent storefront stays dormant.
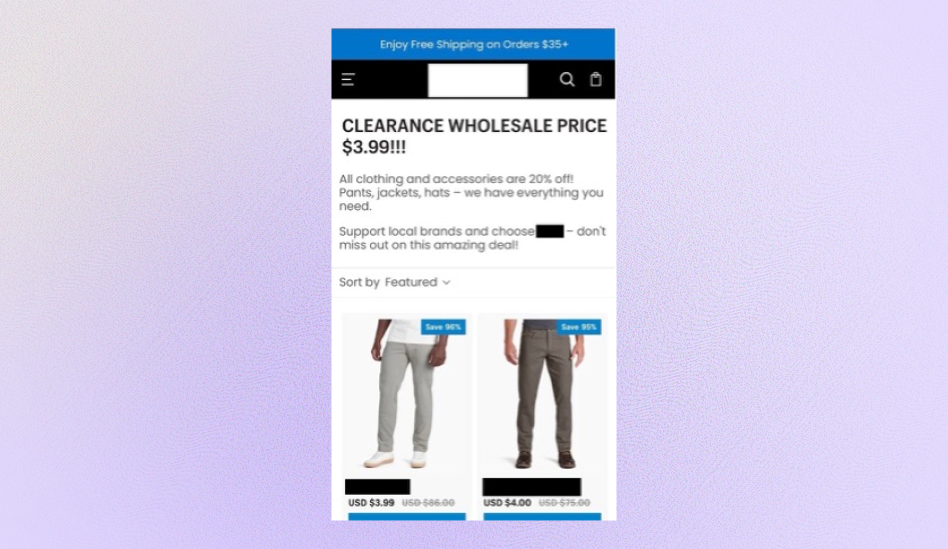
Same domain accessed using the parameters while using iPhone or US proxy
That creates a critical dependency: the scam only comes alive when a victim arrives through a paid ad. Direct URL access, manual browsing, automated crawling? None of it triggers the impersonation content.
Why Desktop-Based Detection Misses the Mark
This multi-layer gating gives the framework significant evasion advantages against conventional brand monitoring:
Automated crawlers running from desktop environments never see the impersonation content. Region-neutral scanning systems get served the fallback storefront. Direct navigation without ad-linked parameters doesn’t trigger fraud delivery.
For security teams relying on traditional domain-based discovery and desktop crawling, these campaigns are effectively invisible. The fraud infrastructure isn’t inactive. It’s selectively active, and built to exclude exactly the kind of traffic that brand protection tools generate.
This Isn’t a One-Off. It’s a Reusable Framework.
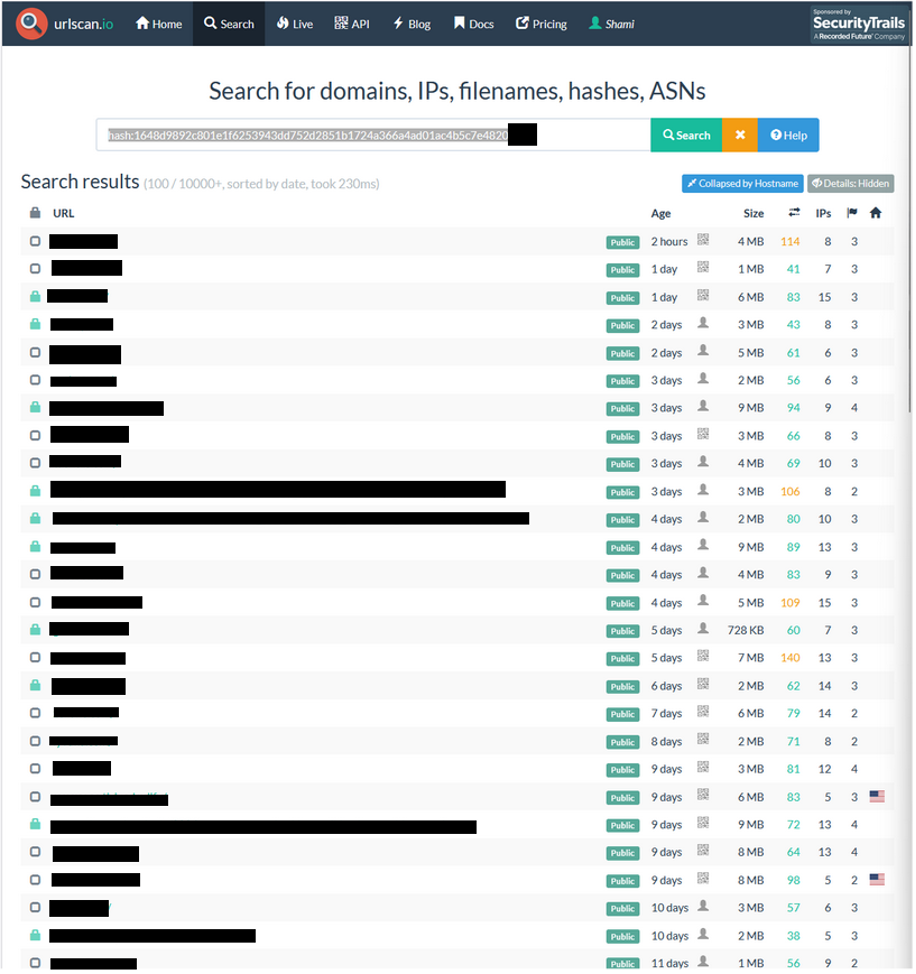
Bolster AI’s passive OSINT expansion found that this activity extends well beyond isolated scam instances. Multiple domains exhibited consistent behavioral and infrastructural characteristics, including disposable domains configured for single-brand impersonation, centralized reuse of the cloaking logic, and repeatable deployment patterns aligned with advertising-driven campaign lifecycles.
The evidence points to a reusable fraud framework capable of rapid reconfiguration and redeployment across multiple brand targets. When one campaign runs its course, the operators spin up the next one using the same playbook.
What Effective Detection Actually Requires
Identifying these campaigns demands a fundamentally different approach to monitoring. It requires victim-environment emulation across targeted geographies, mobile user-agent simulation (specifically iOS profiles), monitoring of paid ad delivery vectors rather than relying on domain-based discovery alone, and artifact-level pivoting through shared resources and infrastructure overlaps.
Without these capabilities, access-controlled impersonation frameworks can continue operating with minimal detection exposure, draining brand equity and defrauding customers in plain sight.
The Bigger Picture: Controlled Exposure Is the New Cloaking
This research highlights a meaningful evolution in fraud delivery. Scam infrastructure is no longer broadly accessible. Instead, it operates under controlled exposure conditions optimized for evasion, scalability, and paid victim acquisition.
Traditional cloaking relied on hiding from search engine crawlers or simple IP blocking. What we’re seeing now is multi-factor access control designed specifically to defeat brand monitoring workflows while maintaining high conversion rates on targeted victims.
For brands and security teams, the takeaway is clear: defensive approaches need to incorporate advertising intelligence and victim-context validation to detect and disrupt campaigns that operate under these constraints. If your detection strategy only works from a desktop browser in a neutral geography, you’re seeing exactly what the scammers want you to see.
Think scams like these might be slipping past your current brand monitoring tools? Bolster AI’s platform detects cloaked impersonation campaigns that traditional desktop-based scanning misses, using victim-context emulation, mobile user-agent simulation, and ad-vector monitoring to surface threats before they reach your customers. Book a demo to see what your current tools aren’t catching.





