By understanding the hacking threats hyperlinks pose and taking proactive…
76 results for keyword "Phishing"
How to Check for Spoofed Emails in Outlook
Key Takeaways Examine email headers via “View message source” for…
6 of the Best Anti-Phishing Software Choices to Protect Your Business
Phishing and online scam sites have become exceedingly sophisticated in…
A Deep Dive into Evilginx
Key Takeaways: Evilginx is a Man-in-the-Middle phishing framework that proxies…
Are Web Beacons Dangerous?
Key Takeaways: Web beacons are not inherently dangerous—they’re neutral technical…
Beyond the Perimeter: Securing Your Brand with Customer-Focused Phishing Defense
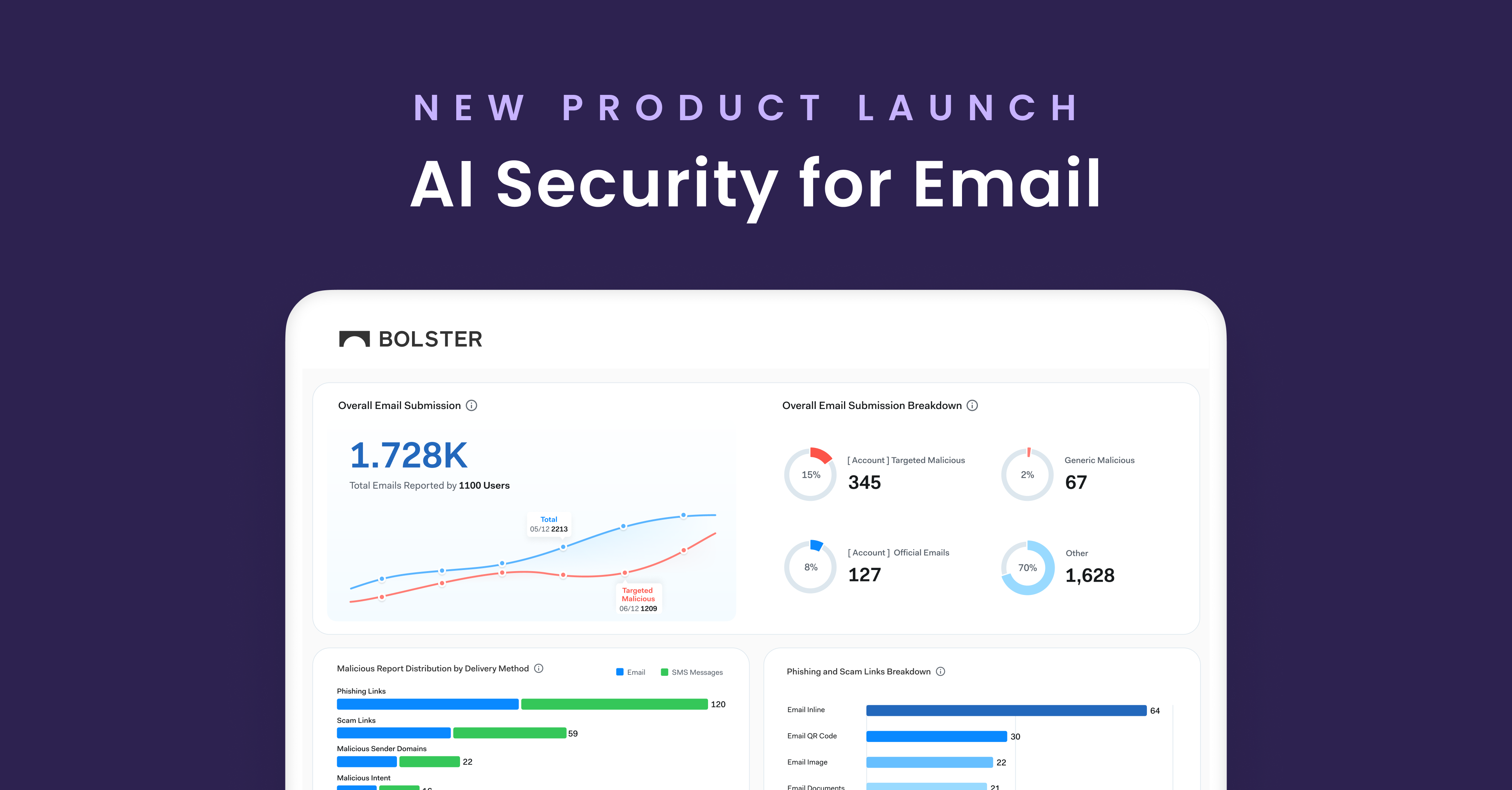
Email continues to be a primary vector for phishing and…
Credit Union Scams: How Cybercriminals Are Targeting Small Credit Unions in the US
In recent months, Bolster’s research team has identified a surge…
Understanding Domain Reputation Attacks and How to Protect Your Brand
Without even defining the term, you could probably guess that…
Understanding Prepending and Its Role in Cybersecurity Attacks
Key Takeaways: Prepending adds data to beginning of strings, files,…
In-Session Phishing is Becoming An Advanced Cybersecurity Threat
In-session phishing is a type of attack where cybercriminals target…
Cracking the Shield: Methods Hackers Use to Bypass MFA
Key Takeaways: Simple 2FA bypass exploits improperly enforced endpoints after…
Stopping Wire Fraud Scams Targeting VCs and Limited Partners
Everyone in the world knows if you need money for…