Cybersquatting, a form of domain name abuse, refers to…
18 results for keyword "Domain Protection"
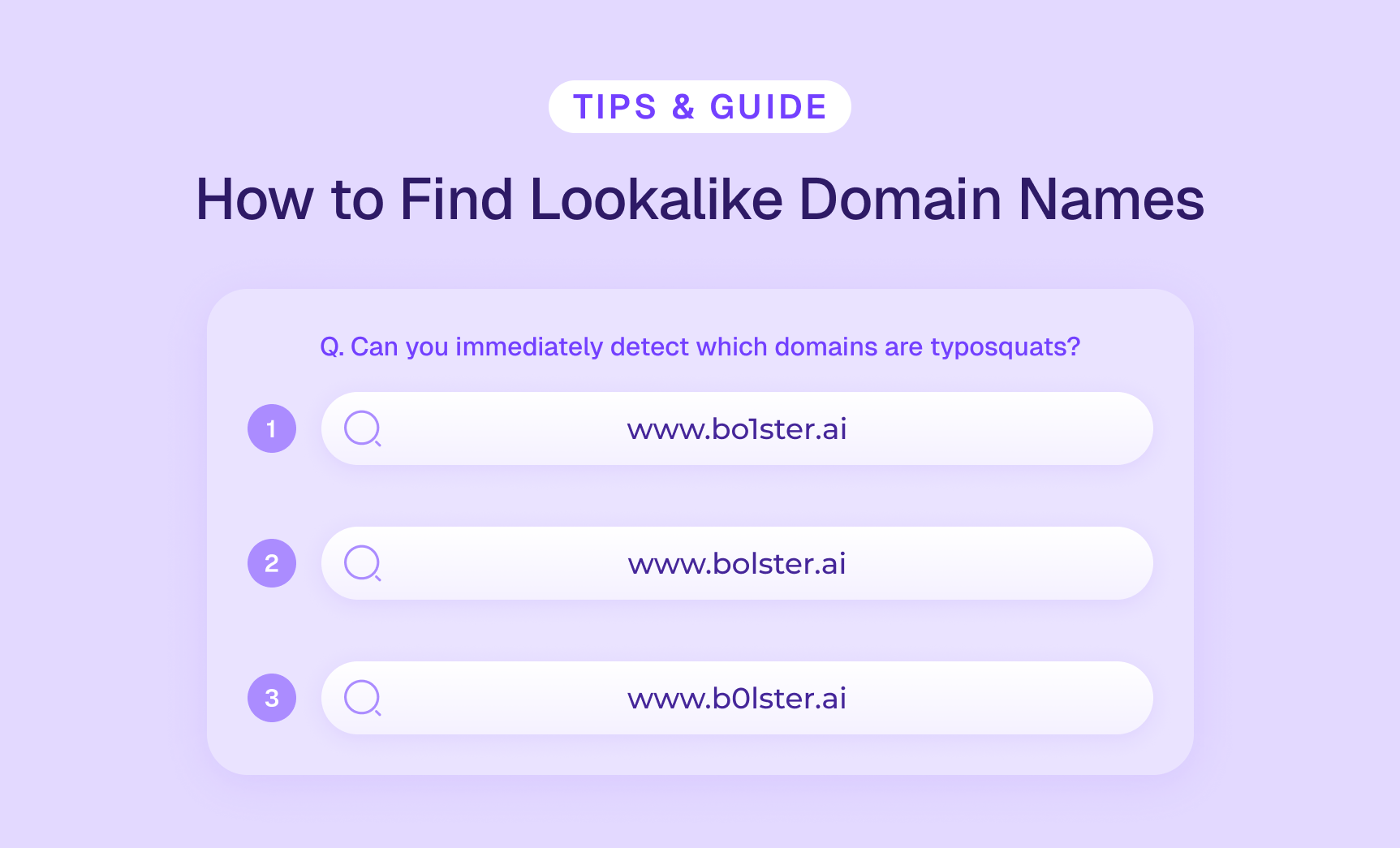
Lookalike Domain Monitoring & How to Find Similar Domain Names
Key Takeaways: Similar domains are fraudulent domains mimicking legitimate ones…
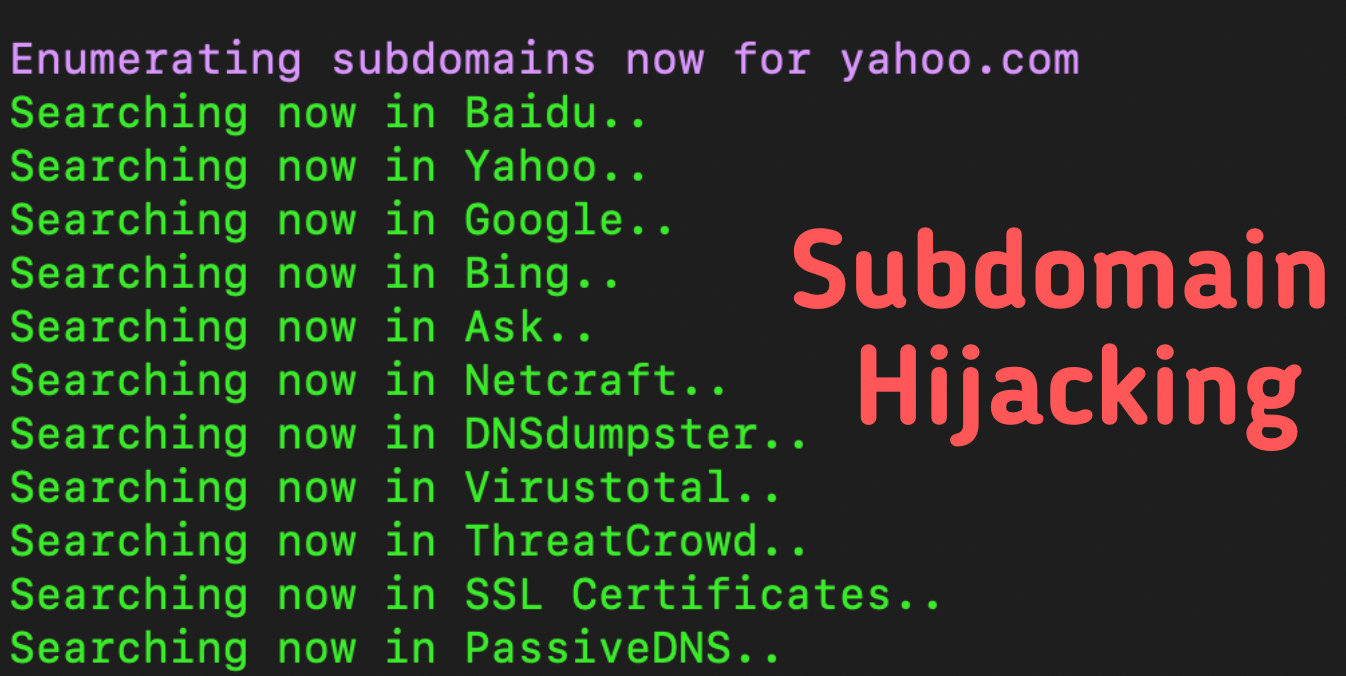
Defining Subdomain Hijacking & How to Identify Subdomains at Risk
Key Takeaways About Subdomain Hijacking: Occurs when attackers control subdomains…
How to Conduct a Website Takedown (The Hard Way), and How to Improve
Key Takeaways: Discover malicious sites through proactive domain risk monitoring…
Understanding Domain Reputation Attacks and How to Protect Your Brand
Without even defining the term, you could probably guess that…
The Full Guide to Protecting Yourself from Fake Sale Websites
Online shopping is no longer a hot trend or something…
Digital Risk Monitoring Importance is Growing Faster Than Ever
Key Takeaways About: Digital Risk Monitoring: DRM automates continuous scanning…
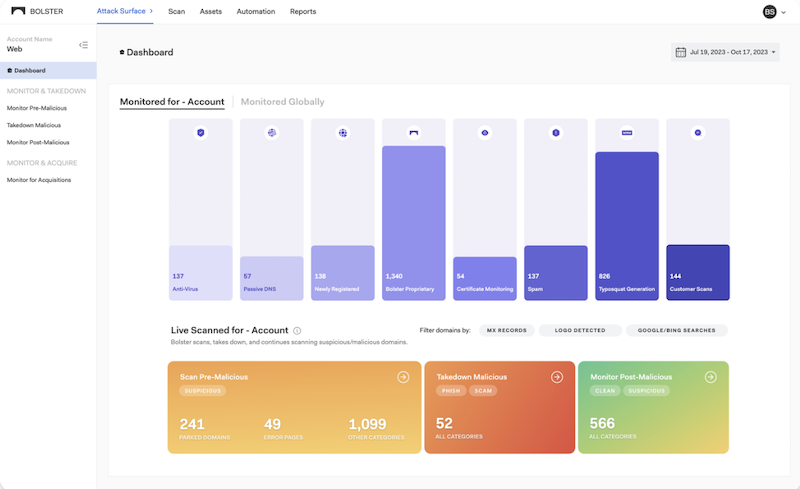
A Visual Journey: Exploring the Redesigned Bolster Dashboard
One of the top challenges that security practitioners often…
The Power of Automated Domain Monitoring
Today, business owners around the world understand that digital…
The Build vs. Buy Dilemma with Domain Risk Management
Domain risks are growing increasingly aggressive, and detrimental to businesses…
Evaluating Web Scraping, Crawling, and Automation with NodeJS Libraries
This blog is part 1 of a web scraping…
How to Conduct a Website Takedown In 3 Easy Steps
Malicious website domains are a headache for organizations to…